Motivation
The Legic Prime system uses proprietary RFIDs for access control to buildings throughout Europe including critical infrastructure such as military installations, governmental departments, power plants, and airports. Despite its use in high security installations, access cards can be cloned from a distance or newly created using a spoofed master token.
Disclosing algorithms
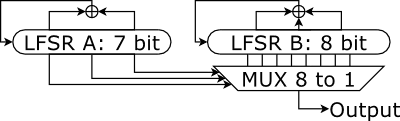
Reverse-engineering secret algorithms from an RFID chip through reconstructing circuits has been demonstrated before when the Crypto-1 cipher was extracted from a Mifare Classic chip. The sole security algorithm we discovered is the following obfuscation function that holds a mere 15 bit of secret state and is seeded with a 6 bit random number (and no secret key!):
Cloning cards
The Legic Prime security systems breaks in two places where cryptography is missing. First, cards and readers do not hold secret keys and cannot authenticate each other, which allows an attacker to assume either role and read, write, or spoof cards and readers. Second, the lack of cryptography enables attacks against Legic’s trust delegation model which places cards in a hierarchy in which higher-level cards can produce lower-level cards. Since no secret information exists that could distinguish higher from lower permission levels, any of the levels can be spoofed for any Legic installation in the world.
Defenses
In the short-term, best practice countermeasures should be implemented in Legic systems.
- A cryptographic signature over the card UID and its identity in the access control system prevents other Legic cards from being used in the system
- Fingerprinting the card communication detects many of the other emulation platforms Even after these quick fixes, the Legic Prime system is not secure enough for access control systems in the long-run. Cards with strong encryption and unique secret keys are needed as a minimum standard.
The concept of organizing access credentials in a trust hierarchy is not flawed in itself. For an implementation of trust delegation to be secure, the delegation process has to be one-way in the sense that only higher level entities are trusted, which again requires a strong function such as a keyed hash or encryption function.
References
The Legic Prime weaknesses were first discussed in a 26C3 talk](https://events.ccc.de/congress/2009/Fahrplan/events/3709.en.html) and further expanded on in a presentation at [EUSecWest 2010.
Functionality to read out Legic cards is available for the Proxmark III RFID tool