In the second half of 2019, Google and a group of mobile operators started implementing a new communication technology, Rich Communication Services (RCS). RCS is poised to replace calling and text messaging for billions of people. It also introduces new messaging possibilities to make native text messaging be more feature-comparable to WhatsApp and iMessage.
RCS is based on internet protocols such as SIP and HTTP to implement group chats, video calls, file transfers and more. SRLabs’ researchers conducted a worldwide survey to estimate security risks in active RCS deployments.
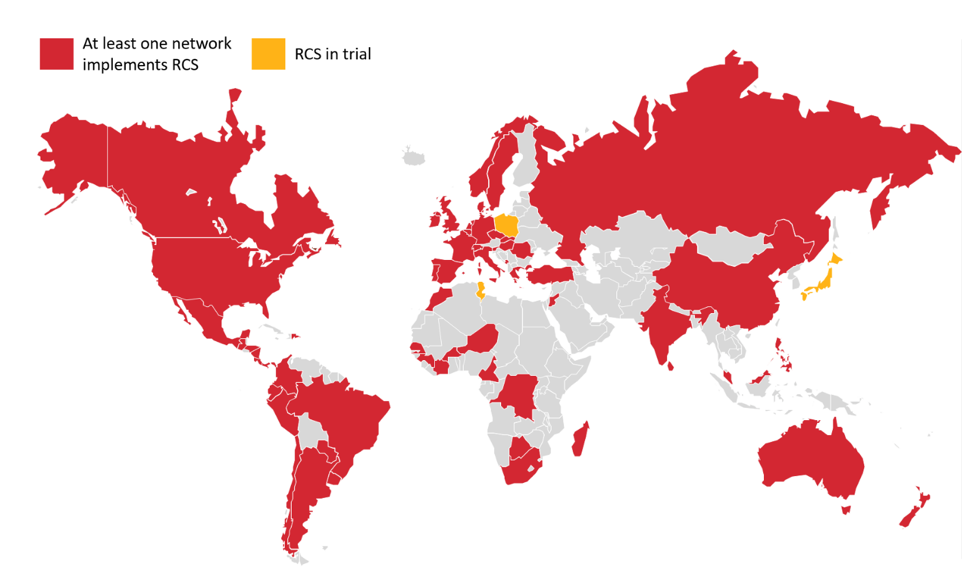
In June 2019, Google officially announced their plans to push RCS on all Android phones starting with trials being run in UK and France. Fast-forward to November 2019, RCS is being rolled out to all Android users in the US, and operators in other countries are running trials. We conducted an internet survey using DNS queries directed to RCS specific domains, confirming the presence RCS servers in many countries.
SRLabs researchers found that a range of different hacking attacks is possible against some RCS deployments. While not all vulnerabilities apply to all networks, these include:
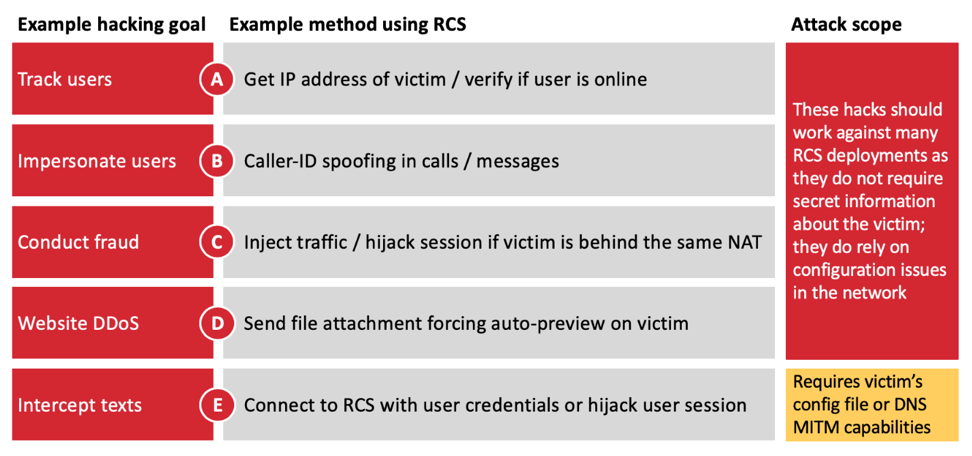
Impersonation (caller ID spoofing), fraud and user tracking can be achieved by criminals without sophisticated equipment or additional target information. Depending on the network configuration, attackers can locally and remotely intercept OTP codes sent via SMS, in attempt to authorize fraudulent bank transactions or take over email accounts. This attack revamps the results obtained by hacking the SS7 network, but at a much lower cost. Details of these hacks will be presented at BlackHat Europe 2019.
These attacks make current RCS deployments as vulnerable to hacking as legacy mobile technologies, such as 2G and SS7. This is surprising for a technology build on Internet technology and under active design.
As one attack example, a local MITM attack allows hackers to intercept and manipulate all user communications. The underlying issue is that the RCS client, including the official Android messaging app, does not properly validate that the server identity matches the one provided by the network during the provisioning phase. This fact can be abused through DNS spoofing, enabling a hacker to be in the middle of the encrypted connection between mobile and RCS network core.
This video demonstrates such an impersonation attack:
This video demonstrates a MITM attack, in which messages can be intercepted and modified:
A demo video showing how a user’s config file can be stolen can be found here:
These vulnerabilities can allow attackers to intercept OTPs that can be used to take control of critical accounts:
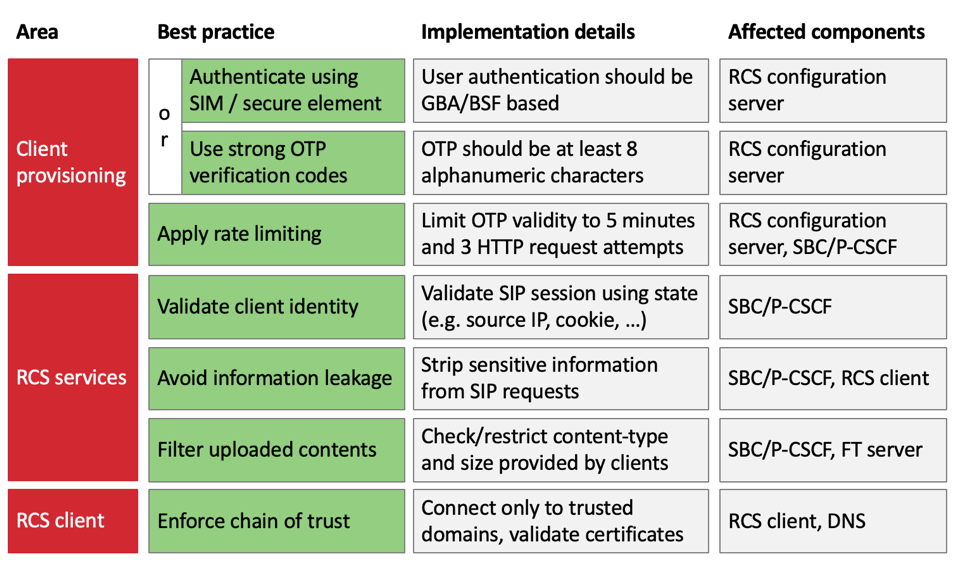
Mobile networks are variably affected by these vulnerabilities depending on gaps in their individual implementations and configuration. All vulnerabilities found relate to common security mistakes that can be mitigated by applying the following best practices:
The full presentation at BlackHat Europe 2019 can be found here.